Head for the hills, folks! It’s not often that we cover security here, but serious times call for serious talk. There is a trojan called Trickbot, and it is one of the stealthiest malware threats in recent memory.
Doesn’t help that it is going after anything and everything that crosses its path.
To fix various Windows 10/11 problems, we recommend Outbyte PC Repair:
This software will repair common computer errors, protect you from file loss, malware damage, hardware failure, and optimise your computer for peak performance. In three simple steps, you can resolve PC issues and remove virus damage:
- Download Outbyte PC Repair Software
- Click Start Scan to detect Windows 10/11 issues that may be causing PC issues.
- Click Repair All to fix issues with your computer's security and performance.
This month, Outbyte has been downloaded by 23,167 readers.
And to make matters worse, this is a rapidly evolving threat. The latest twist in its tale is that it is targeting Windows 10 users specifically via new methods that not only evade but actually disable Windows Defender on these systems.
Read on to see what damage this radical new threat does, and what steps you can take to avoid falling victim to its menace.
The origin of Trickbot
Trickbot may be in the news for all the wrong reasons these days, but this malware is not new. It has been causing trouble since 2016. Since then, this banking trojan is estimated to have compromised no less than 250 million email accounts.
So much so that many in the cybersecurity world consider Trickbot as the top most threat targeting the computing landscape.
This malware is designed with a laser focus on stealing the private data of users. Whether it be harvesting emails or stealing logins and passwords, hijacking web browsers or altering displayed websites, stealing banking details or transferring money out of crypto wallets, Trickbot is doing it all.
Another dubious distinction of this banking trojan is that it, at start, it focused primarily on private banks, wealth management firms and other types of financial institutions.
When it first emerged, its main target were countries in the English-speaking world like US, Canada, and Australia. It has since spread its dark wings over several other markets, including India, Israel, Malaysia, Germany, and other parts of Europe.
Malwarebytes Labs has a pretty good primer up on Trickbot, including its features, symptoms, and sources of infection. Also be sure to give this article a scan for technical details.
Threatpost also has a piece keeping tabs on how this banking trojan has evolved in recent months, and how it has added even more sophisticated and innovative tactics to its nefarious arsenal. This is another quality resource of updated information on Trickbot.
We’ll focus specifically on how this malware has evolved to specifically target unsuspecting Windows 10 users, both at home and business. And how some of the new tricks it has learned along the way allow it to infiltrate even the most guarded of systems.
Trickbot Development
The developers behind Trickbot have updated this malware numerous times over the years, adding advanced new traits every time. One of these features is screen locking, where the more recent versions of Trickbot are capable of locking the computer screens of the victims.
What’s even worse, and an extremely dangerous addition, is the capability of hijacking several different kinds of applications and then stealing credentials, recording information relating to web browsing, as well as system details itself like the CPU, operating system and running processes.
No app is spared. If a program deals with credentials, it is under risk of contamination. Researchers have found that Trickbot is able to easily hijack software like Microsoft Outlook, WinSCP, FileZilla, as well as browsers like Mozilla Firefox, Google Chrome, Microsoft Edge, even Internet Explorer.
It truly is the malware that evolves!
Trickbot vs Windows Defender
It’s not often that a malware takes on Windows Defender and lives to tell the tale. But this is exactly what makes Trickbot one of the most dangerous trojans out there in the wild right now. It has several stealthy tricks up it sleeves in how it targets Windows 10.
Goes without saying that this the most secure and watertight version of the OS that Microsoft has created. It comes with advanced security features, and a highly capable baseline defense out the box in the form of Windows Defender.
How Trickbot runs circles around it is a true cause for concern.
Trickbot comes with a specific skillset that targets Windows 10 users that rely upon Windows Defender to protect their machines from malware threats — and there are a lot of them.
According to the latest figures from Microsoft, more than half the user base relies on Windows Defender for system protection. 50% here means more than half a billion users. This native, built-in security solution grows in strength every new moon. But even this reliable line of defense has been breached by newer versions of Trickbot.
Trickbot is so sophisticated that it not only detects Windows Defender, but was found to be employing at least 17 steps in its attempt to incapacitate it altogether!
These include disabling and deleting the WinDefend service, terminating the processes associated with Windows Defender, stopping its real-time protection, deactivating security notifications, adding a policy to automatically disable the Windows Defender components.
Not the ones to be stopped, the malware authors recently added a dozen new tricks in order to prevent Windows Defender from protecting Windows 10 users. These range from modifying the registry and using PowerShell commands.
How to Stop Trickbot
Fighting against malware is always a major struggle, particularly for power users that spend their days online and businesses that stay connected with the world. But the most important factor is knowing what kind of threat you are dealing with.
Only then come the next steps of preventive actions.
For most users, following the general security best practices is the best place to start.
Good mitigation advice is to block access to Windows Registry, first and foremost. Another important step to take is to ensure that whoever is using the computer does not have administrator rights by default — all malware strands thrive on elevated privileges.
Then there is AppLocker.
It is something that comes in the tin with Windows 10, but the average user is blissfully unaware of the potential of this feature. It basically lets you control which apps and files can run on your system, and these include executable files, dynamic link libraries (DLLs), packaged apps, packaged app installers, Windows installer files and even scripts.
Essentially, using AppLocker, you can allow only authorized software to run on your PC. In spite of that, this remains a very powerful yet underused feature of the operating system.
Also look at the Windows Tamper Protection feature, and set it up to block attempts to modify the Windows Defender settings through the registry.
Trickbot does not really bypass Tamper Protection on Windows 10, so as long as this feature is turned on by default on your system, you should be relatively safe from having Windows Defender disabled by this pesky malware.
All these steps are no substitute of recommend best practices for computing security. These involve habits like never wandering off to suspicious sites, not installing distrustful programs, and never opening mail attachments from unknown senders.
What to do if I have been infected?
Detecting the Trickbot virus can be hard, so your best bet is to reduce the probability of hijack via this malware. Since this trojan attaches itself to a free application, even installing a new media player can lead to infection. In fact, such programs are the likeliest carriers of this malicious threat.
Cleaning up infected systems, likewise, is a difficult and complicated proposition, as this malicious program does a good job of imitating legitimate computer processes and files. The virus is also capable of updating itself after the infection, meaning each victim will have the newest version of Trickbot when they connect to the Internet.
Run a full system as scan after updating your security software and then follow the recommendations provided. Most antimalware solutions now identify this threat.
Microsoft is also on top of things with Trickbot.
According to the Windows maker, the latest version of Windows Defender protects against newer variants of this malware. Users that have applied the latest updates to the security suite, or those who have automatic updates enabled are protected.
That said, since Trickbot is a lot more persistence than most other malware, you are still in danger if you have not turned on the Tamper Protection setting on your Windows 10 system. Some users disable this feature in order to avoid conflict with a third-party security application. If you count yourself among these, then your computer and your personal information remain at high risk.
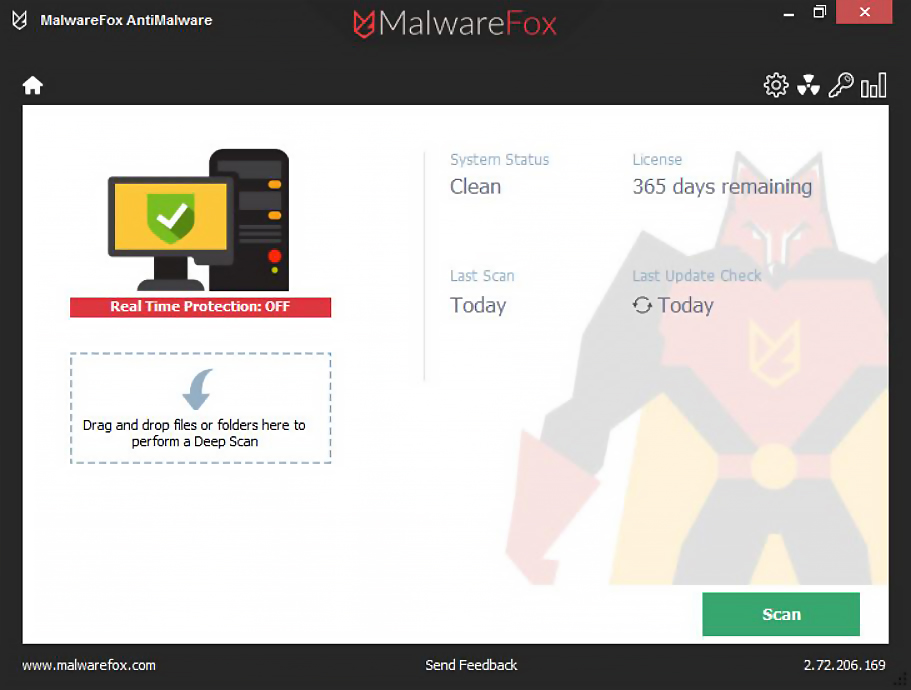
- Malware Detection and Removal
- Anti-Spyware and Anti-Adware
- Browser Hijacker Remover
- Ransomware Protection
- Lightweight / Cloud based
Conclusion
Banking trojans have been around forever, and they are not going away as long as the world uses the web for money transactions. But what makes Trickbot so scarily special is how quickly it has evolved and how even Microsoft is having a hard time keeping up with its tricks.
The authors behind this malware have used various methodologies to evade detection by security software, and prevent Trickbot from being neutered. This makes this trojan among the more sophisticated threats seen across the years.
One that goes the extra mile, particularly on Windows 10.
Shawn is a WindowsChimp Staff writer, who is a fan of making lists and does the same on this site. He has a Contemporary Writing degree and been in technology niche since last 3 years.


Well thank you for this information. Even though they say to only use one malware I have three. Malware hunter, malware killer, and Malwarebytes. I also use Kaspersky total security. But from what I understand is you can still get this malware.. well thank you for all your doing.
look at the Windows Tamper Protection feature, and set it up to block attempts to modify the Windows Defender settings through the registry.
How? I searched for tamper protection, setting was not found?
I also keep getting a an error. 0x80070015 when windows tries to updates?
Windows security then Virus & threat protection, virus & threat protection settings and Tamper Protection is 4th one down